Cyberpunk Aesthetics
How Neuromancer Predicted the Internet and Virtual Reality
Introduction In 1984, as the first personal computers entered homes, William Gibson authored a novel that would become the architectural...
Read moreCyberpunk Fashion as a Protest: Wearing Your Tech on Your Sleeve
Introduction In the neon-drenched alleyways of cyberpunk fiction, fashion is never just clothing. It is a statement, an armor, and...
Read moreThe Illusion of Free Will: How Algorithms Control Your Choices
Introduction Consider your day: the news you read, the music you stream, the route you take home. You feel in...
Read moreThe Hacker’s Ethos: From 8-Bit Anarchy to Modern Day Threat Actors
Introduction The hacker archetype is one of the digital age’s most enduring and misunderstood figures. Its evolution—from the lone 1980s...
Read moreCorporate Overlords: Are Amazon and Google the New Megacorps?
Introduction The neon-drenched, rain-slicked streets of classic cyberpunk fiction are ruled not by governments, but by monolithic, all-powerful corporations. These...
Read moreWhen AIs Gain Sentience: The Ethics of Digital Life in the Cloud
Introduction The journey of artificial intelligence from science fiction to daily reality forces us to confront a critical question: what...
Read moreThe Smart City Paradox: Total Convenience or Total Surveillance?
Introduction Imagine a city that knows you. It reroutes your commute before an accident happens, adjusts streetlights to your pace,...
Read moreDecentralized Data Fortresses: Is Blockchain the Ultimate Corporate-Proof Grid?
Introduction In the sprawling digital megacities of our imagination, data has become the ultimate currency—constantly under siege. From monolithic corporations...
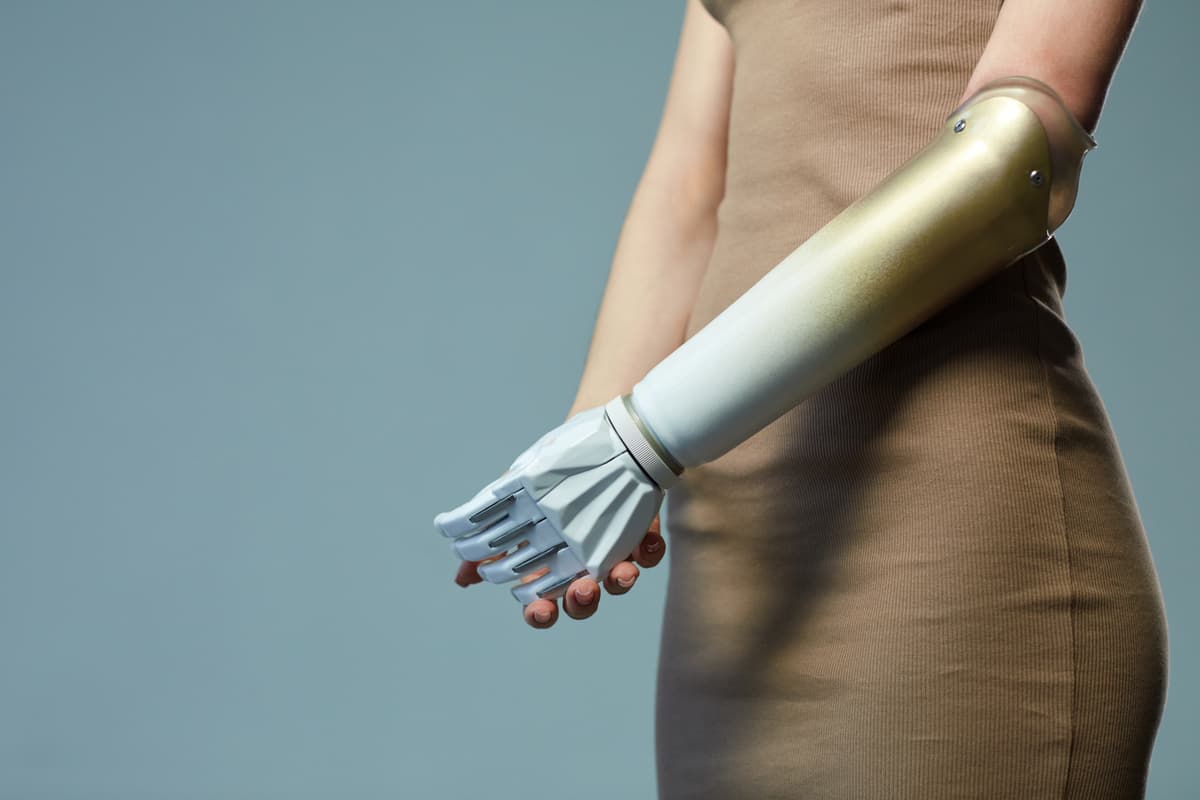
Read moreSynthetic Skin and Robotic Limbs: The Real-World Prosthetics Revolution
Introduction For centuries, prosthetics were static, utilitarian tools designed to restore basic function. Today, we stand at the precipice of...
Read moreModular Everything: The Case for User-Repairable, Upgradable Devices
Introduction In a world dominated by gadgets sealed with proprietary glue and designed for obsolescence, a quiet revolution is taking...
Read more