Cyberpunk Aesthetics
The Rise of Bio-Integrated Tech: From Smartwatches to Neuralink
Introduction We are witnessing a fundamental shift in how we connect with the digital world. The age of external gadgets...
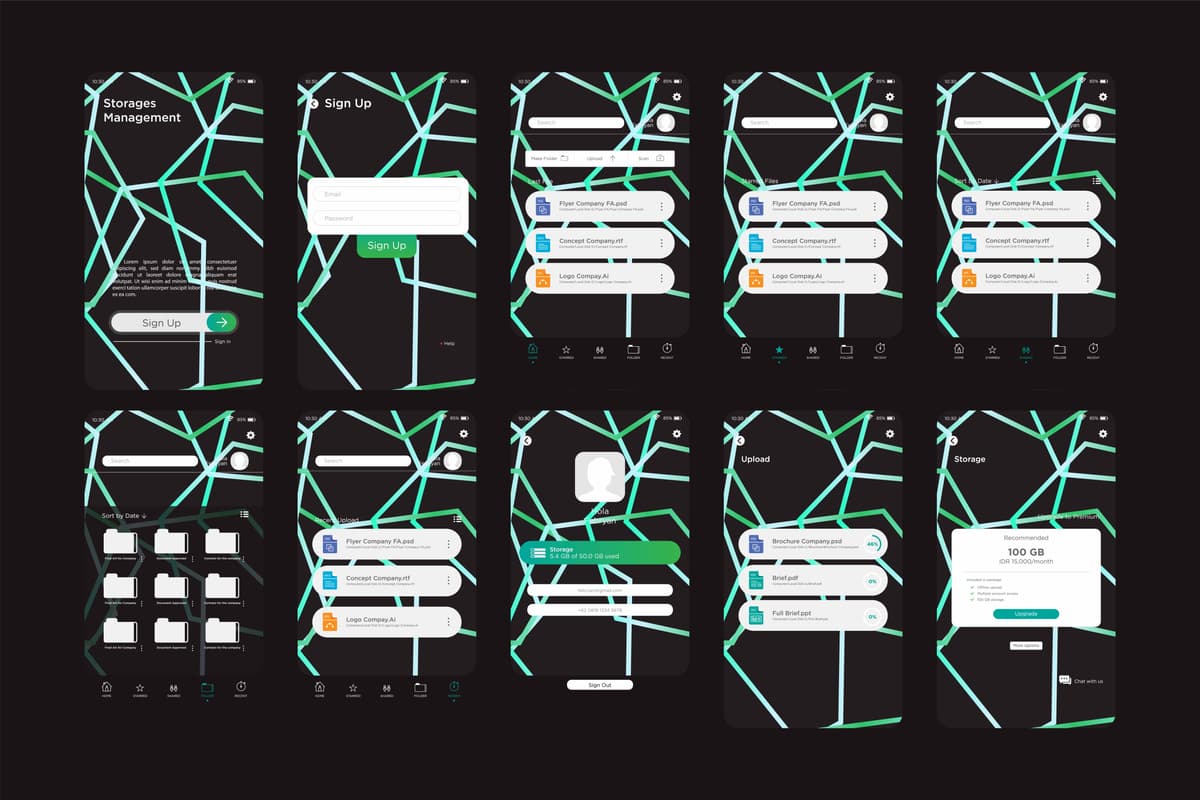
Read moreMinimalism is Dead: Why Cluttered, Data-Dense UIs are Making a Comeback
Introduction For years, the design world swore by minimalism: clean lines, empty space, and the mantra of “less is more.”...
Read moreBeyond the Screen: Bringing Holographic UI and HUDs into the Real World
Introduction For decades, the shimmering, translucent interfaces of science fiction have captivated our imaginations. From tactical fighter cockpit displays to...
Read moreKitsch vs. Chrome: Deconstructing the “High Tech, Low Life” Design Principle
Introduction In the sprawling, rain-slicked cityscapes of cyberpunk, a single design principle acts as the genre’s beating heart: “High Tech,...
Read moreThe Typography of Tomorrow: Why Monospaced and Glitch Fonts Reign Supreme
Introduction In the sprawling digital cityscapes of our imagination, where neon bleeds into rain-slicked streets, the written word is an...
Read moreNeon Genesis: How RGB Lighting Became the New Grime
Introduction In the sprawling, rain-slicked cityscapes of cyberpunk, light is more than illumination—it’s identity, pollution, and atmosphere. The aesthetic is...
Read more💻 20 Cyberpunk Aesthetics Article List (Title + Description)
Introduction Step into a world where neon bleeds into rain-slicked asphalt and the line between human and machine is irrevocably...
Read moreHere is your list of 20 Cyberpunk Aesthetics Article Titles with their corresponding descriptions:
Introduction Cyberpunk is more than a genre; it’s a visual and philosophical language for our modern anxieties. It speaks directly...
Read moreThat clarifies things perfectly. You need a simple, clean list of titles with a short, descriptive summary of the article’s content in brackets.
Introduction Welcome to the neon-drenched, rain-slicked alleyways of the future. The cyberpunk aesthetic, born from the literary foundations of William...
Read more