Introduction
From play to strategy: why it matters now
Entertainment has entered a strategic era. Game theory and competitive AI now shape skill-based matchmaking (SBMM), in-game economies, branching narratives, and dynamic pricing. Systems that learn and adapt keep audiences engaged longer while reducing guesswork in design.
The shift is treating rules as tunable systems with clear objectives, not one-off choices. Inspired by research like Microsoft’s TrueSkill and public operator posts, teams turn “balance patches” into measurable, reversible policy updates that can be tested, rolled back, and improved.
What this covers and who it’s for
This guide serves product leaders, game designers, data scientists, producers, and media strategists who want practical, safe-to-ship playbooks. You’ll learn core concepts, patterns that generalize, and a pilot plan you can run in one to two sprints.
We cover strategic foundations, how AI as co-strategist changes design, ethical and business guardrails, and a stepwise rollout. References map to established sources (e.g., TrueSkill, Vickrey auctions, AlphaGo, OpenAI Five, GDPR/CCPA) so guidance remains portable and verifiable.
The strategic foundations of game theory
Payoffs, equilibria, and incentives
Game theory models players, payoffs, and information. In practice, “players” include users, creators, teams, and algorithms. Payoffs span fun, status, rewards, and revenue. Most live environments are incomplete-information games, so beliefs and signaling matter as much as raw skill.
Designers seek stable outcomes—Nash equilibria—where no one can improve unilaterally. The craft is nudging incentives so stability stays engaging, not stale. Soft caps, diminishing returns, cooldowns, visibility controls, and clear counters keep metas diverse without heavy-handed nerfs.
Mechanism design: rules shape outcomes
Mechanism design flips the lens: choose rules so rational behavior yields healthy results. Draft picks can discourage super-teams; SBMM reduces smurfing; second-price or VCG auctions align ad spend with true value. Uncertainty-aware ratings like TrueSkill often pair better than raw ELO.
Trust is a feature. Explain progression and odds, and show high-level matchmaking factors without exposing exploits. Cap rating volatility, test for collusion, and monitor wealth inequality (e.g., Gini) so sink/source mismatches or farming loops are caught before they damage the economy.
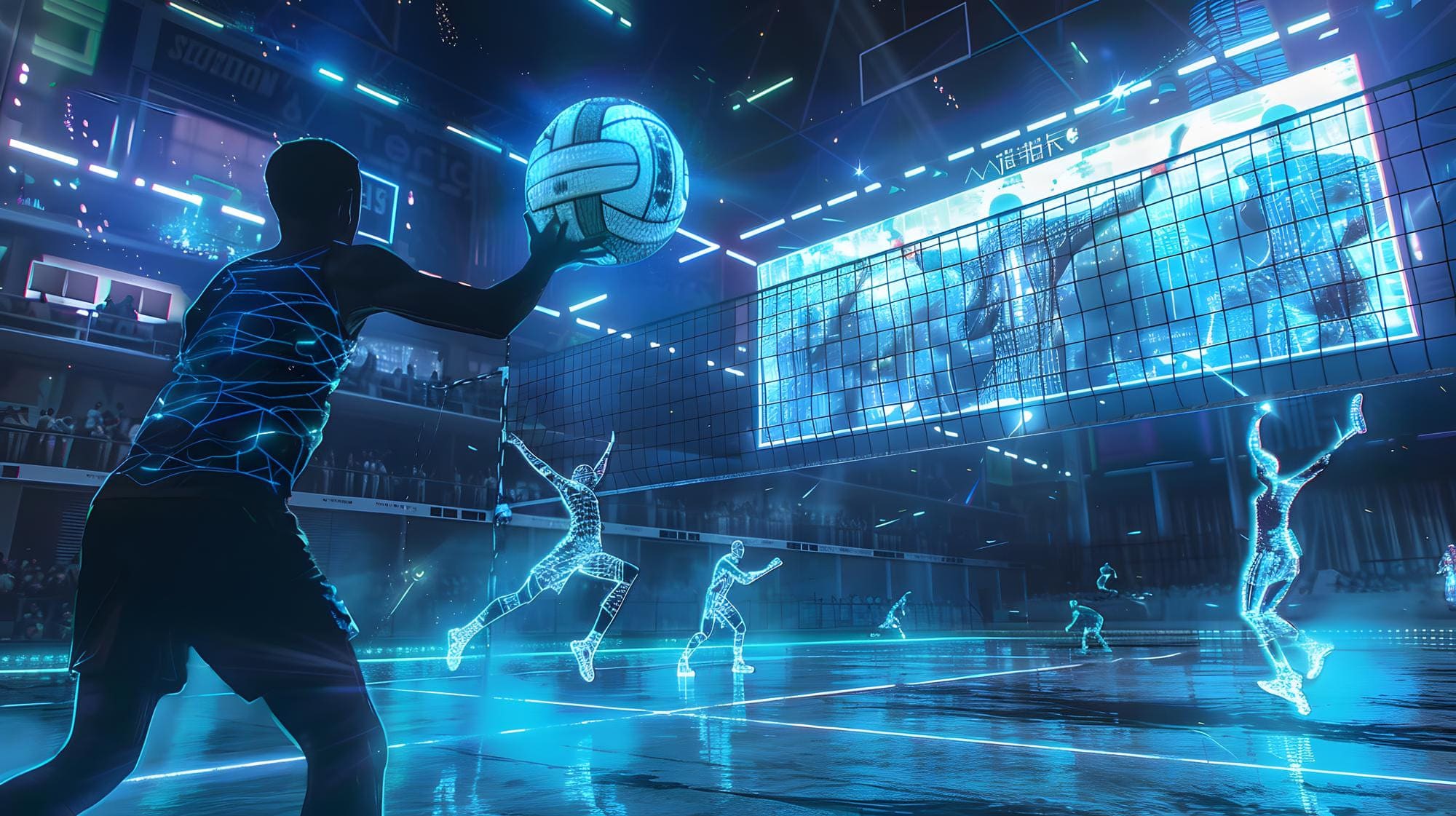
Competitive AI as co-strategists
Reinforcement learning and self-play
Modern reinforcement learning (RL) learns by trial, reward, and policy update. In self-play, agents spar with themselves, surfacing tactics no human encoded. This improves balance testing, stress-tests rules, and probes edge cases before players find them.
Production stacks favor curriculum learning, entropy regularization, and KL-constrained updates (e.g., PPO/TRPO) for stability. Use off-policy evaluation on logs, adversarial tests, and human-in-the-loop gating before live. Lessons from AlphaGo and OpenAI Five prove the power—if you avoid overfitting to narrow metas.
Human–AI rivalry and collaboration
AI should augment, not replace. Think coaches that explain “why,” casters that surface live stats, or sparring partners that mirror your style. Explanations beat prescriptions and reduce automation bias: “we recommend X because your last 10 games show Y,” with opt-outs.
Calibrate assistance by context (ranked versus casual), and audit for disparate impact across regions and platforms. Log model versions, inputs, and decisions with immutable audit trails, especially for moderation and rewards, to support appeals and compliance.
Design and monetization in the AI era
Dynamic economies and engagement loops
AI-powered economies adjust drop rates, prices, and quests to sustain healthy circulation. Game-theoretic thinking prevents arms races: cap runaway advantages, subsidize comeback mechanics, and keep multiple strategies viable so one grind does not crowd out fun.
Track money supply, sink/source balance, inflation, and wealth distribution. Aim for sinks/sources near 1.0 over a season, investigate sudden spikes, and constrain price changes. Value-based pricing and personalized bundles can lift ARPDAU—if offers are fair, clear, and useful.
Fairness, transparency, and wellbeing
Competitive systems can pressure players into unhealthy loops. Bake in safety by design: cool-downs, opt-in difficulty escalations, playtime nudges, and content filters. Make odds visible, explain high-level matchmaking logic, and provide easy off-ramps.
Ethics reduces risk. Obtain consent, minimize data, and set retention limits aligned with GDPR/CCPA. Audit toxicity and model decisions with calibrated thresholds plus human moderation. Publish change logs so communities see what changed, when, and why.
Actionable playbook
Start small: a six-week pilot
Select one high-impact loop—matchmaking, economy tuning, or ranked progression—and define success and kill criteria up front. Prepare a shadow-control policy, a rollback SLO tied to retention and toxicity, and pre-brief support and community teams.
Simulate with historical data, then canary to 1–5% of traffic behind feature flags. Add guardrails (MMR deltas, rate limits, price floors/ceilings). Iterate weekly with quantitative metrics and qualitative feedback; prefer well-behaved optimizers with explicit constraints.
Measure what matters
Tie success to long-term retention, fairness proxies, and community health—not just revenue spikes. Use calibration plots for win probability, variance of match quality, inequality measures for economy health, and distributional views to avoid masking harm to subgroups.
Reduce p-hacking with pre-registered analyses, off-policy estimators (IPS/DR), and counterfactual replays. Track feature drift (e.g., SHAP summaries, PSI) and keep immutable logs of models and parameters so you can audit, explain, and roll back fast.
Conclusion
Key takeaways
Game theory supplies the language of incentives; competitive AI supplies adaptability. Together, they produce fairer, stickier, and more profitable experiences—when guardrails, transparency, and player value come first. Design rules as levers and measure outcomes holistically.
Favor stable mechanisms, explainable assistants, and reversible policies. Use audits and change logs to sustain trust. Short-term revenue gains are worthless if churn and toxicity rise; optimize for durable engagement and community health.
Call to action
Choose one loop, design guardrails, and launch a six-week pilot. Define the objective in one sentence, pick a primary metric with thresholds, and set clear rollback paths. Treat every release as an experiment and every experiment as a learning asset.
Start now: assemble a design–data–ops trio, pre-register your evaluation, and ship a canary. Cite public standards and research where relevant (TrueSkill, Vickrey auctions, AlphaGo, OpenAI Five), and adapt to your platform and regional requirements.